The WannaCry ransomware struck across the globe in May 2017. Learn how this ransomware attack spread and how to protect your network from similar attacks.
Symantec has uncovered two possible links that loosely tie the WannaCry ransomware attack and the Lazarus group:
While these findings do not indicate a definite link between Lazarus and WannaCry, we believe that there are sufficient connections to warrant further investigation. We will continue to share further details of our research as it unfolds.
A virulent new strain of ransomware known as WannaCry (Ransom.Wannacry) has hit hundreds of thousands of computers worldwide since its emergence on Friday, May 12. WannaCry is far more dangerous than other common ransomware types because of its ability to spread itself across an organization’s network by exploiting a critical vulnerability in Windows computers, which was patched by Microsoft in March 2017 (MS17-010). The exploit, known as “Eternal Blue,” was released online in April in the latest of a series of leaks by a group known as the Shadow Brokers, who claimed that it had stolen the data from the Equation cyber espionage group.
Symantec Endpoint Protection (SEP) and Norton have proactively blocked any attempt to exploit the vulnerability used by WannaCry, meaning customers were fully protected before WannaCry first appeared.
The Blue Coat Global Intelligence Network (GIN) provides automatic detection to all enabled products for web-based infection attempts.
Symantec and Norton customers are automatically protected against WannaCry using a combination of technologies.
Proactive protection was provided by:
Customers should have these technologies enabled for full proactive protection. SEP customers are advised to migrate to SEP 14 to take advantage of the proactive protection provided by Machine Learning signatures.
Network-based protection
Symantec has the following IPS protection in place to block attempts to exploit the MS17-010 vulnerability:
SONAR behavior detection technology
Sapient Machine Learning
Antivirus
For expanded protection and identification purposes, the following Antivirus signatures have been updated:
Customers should run LiveUpdate and verify that they have the following definition versions or later installed in order to ensure they have the most up-to-date protection:
The following IPS signature also blocks activity related to Ransom.Wannacry:
Organizations should also ensure that they have the latest Windows security updates installed, in particular MS17-010 to prevent spreading.
WannaCry searches for and encrypts 176 different file types and appends .WCRY to the end of the file name. It ask users to pay a US$300 ransom in bitcoins. The ransom note indicates that the payment amount will be doubled after three days. If payment is not made after seven days, the encrypted files will be deleted.
Decryption of encrypted files is not possible at present. If you have backup copies of affected files, you may be able to restore them. Symantec does not recommend paying the ransom.
In some cases, files may be recovered without backups. Files saved on the Desktop, My Documents, or on a removable drive are encrypted and their original copies are wiped. These are not recoverable. Files stored elsewhere on a computer are encrypted and their original copies are simply deleted. This means they could be recovered using an undelete tool.
WannaCry first appeared on Friday, May 12. Symantec saw a dramatic upsurge in the number of attempts to exploit the Windows vulnerability used by WannaCry from approximately 8:00 GMT onwards. The number of exploit attempts blocked by Symantec dropped slightly on Saturday and Sunday but remained quite high. Exploit numbers increased on Monday, presumably as people returned to work after the weekend.
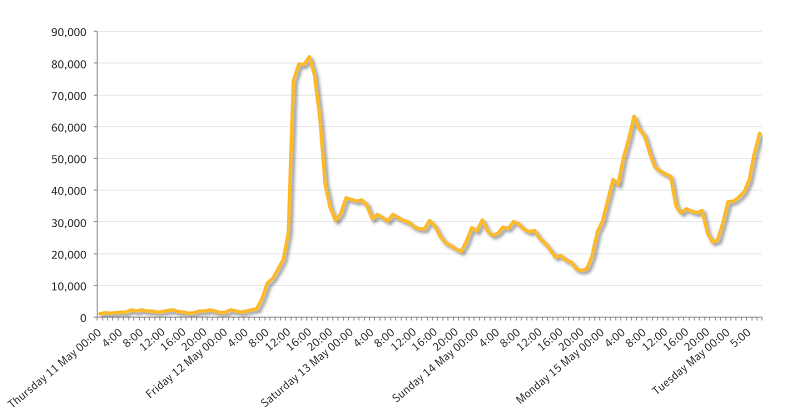
Figure 1. Number of exploit attempts blocked by Symantec of Windows vulnerability used by WannaCry per hour
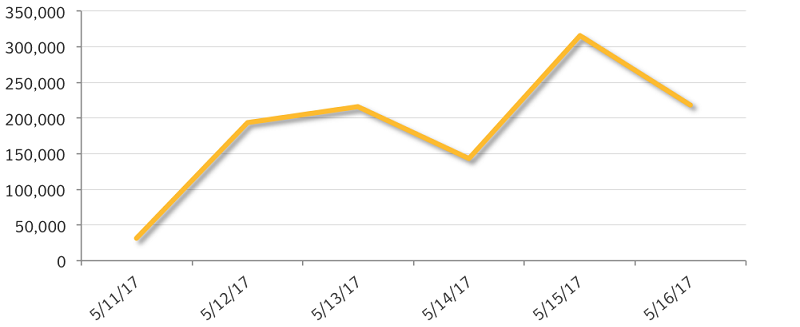
Figure 2. Number of exploit attempts blocked by Symantec of Windows vulnerability used by WannaCry per day
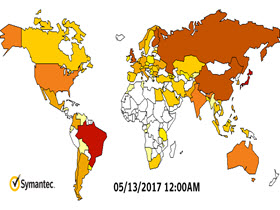
Figure 3. Heatmap showing Symantec detections for WannaCry, May 11 to May 15
Any unpatched Windows computer is potentially susceptible to WannaCry. Organizations are particularly at risk because of its ability to spread across networks and a number of organizations globally have been affected, the majority of which are in Europe. However individuals can also be affected.
No, this is not believed to be a targeted attack at this time. Ransomware campaigns are typically indiscriminate.
WannaCry has the ability to spread itself within corporate networks without user interaction, by exploiting a known vulnerability in Microsoft Windows. Computers that do not have the latest Windows security updates applied are at risk of infection.
While WannaCry can spread itself across an organization’s networks by exploiting a vulnerability, the initial means of infection—how the first computer in an organization is infected—remains unconfirmed. Symantec has seen some cases of WannaCry being hosted on malicious websites, but these appear to be copycat attacks, unrelated to the original attacks.
Analysis of the three Bitcoin addresses provided by the attackers for ransom payment indicate that at the time of writing, a total of 31.21 bitcoin ($53,845) had been paid in 207 separate transactions.
Leave a Reply